What if the easiest way into your organization isn’t a technical exploit, but instead a simple human interaction?
This was the question at the heart of today’s Special Topics presentation, the second in the our technical series. Focused on exploring how threat actors leverage AI and human behaviour to gain access to your sensitive systems, this session explored what a real physical attack might look like.
Cybersecurity is About More Than Technology & Tools
One of the strongest takeaways from the presentation was that cybersecurity isn’t only about tools. While controls like firewalls and security systems are essential, they can be quietly undermined by gaps exposed by simple, everyday habits. Security posture is as much about properly training your people and establishing effective processes as it is about your systems.

From left to right: Frank Fazio (founder of CySat Security Inc.), Joanne Soave (CEO), Aislyn Laurent (ICT Research Analyst), Laura McCabe (Senior Project Manager), Navraj Toor (Business Analyst)
Threat Actors Target Human Behaviour
Frank lead the group through real-world examples of physical attacks, highlighting how small procedural gaps in routines open the door to attackers (often literally). These attacked weren’t made possible by dramatic system failures, but instead because of subtle oversights. He discussed how seemly mundane protocols like badge checks and visitor sign-in sheets can prevent breaches at the source.
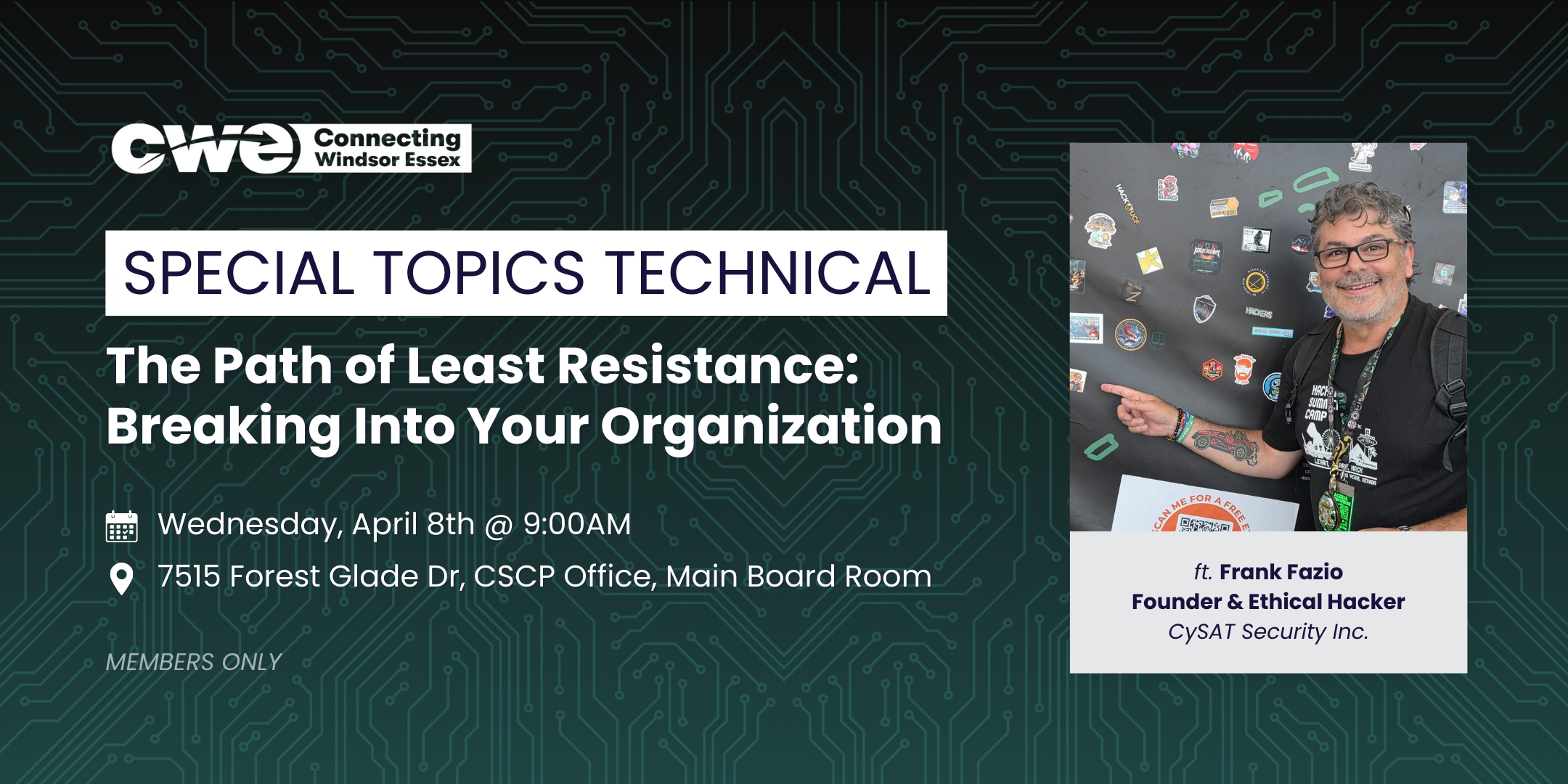
Spotlight on Our Facilitator: Frank Fazio
A big thank‑you goes to our facilitator, Frank C. Fazio. As the Founder of CySAT Security Inc., and an ethical hacker, Frank offers comprehensive and approachable cybersecurity training for organizations of all sizes. His ability to turn real attack techniques into clear, relatable lessons made complex concepts easy to grasp and sparked meaningful discussion among participants.
Coming Up Next
We’re also grateful to everyone who joined, asked thoughtful questions, and shared their perspectives. Our Special Topics series is a consistent reminder that strengthening our regional cybersecurity posture starts with empowering people with awareness and understanding. We’re looking forward to continuing that conversation in future CWE events – members stay tuned!
Meaningful, stress free change starts with engaging your team in collaborative communication. Find out how CWE can facilitate the those conversations by learning more about membership today.